Here’s an article on stopping threat scanning, employing the second-person point of view:
You’re likely reading this because you’ve encountered it: the relentless probing of your network. Whether you’re a seasoned administrator or just starting to grapple with cybersecurity, the constant hum of threat scanning can be unnerving. It’s the digital equivalent of someone trying every lock on your house, every day. Understanding why it happens and, more importantly, how to effectively stop it is crucial for maintaining the integrity and security of your digital assets. This isn’t about panicked reactions; it’s about implementing strategic, methodical defenses.
Threat scanning, at its core, is the process by which malicious actors or automated tools search for vulnerabilities. This can range from rudimentary scans for open ports to sophisticated attempts to exploit known software flaws. The goal is usually to identify an entry point, a weakness that can be leveraged for their advantage, be it data theft, system disruption, or any number of illicit activities. Ignoring these scans is a gamble you can’t afford to take. Proactive defense is not an option; it’s a necessity.
Understanding Your Adversary: The Scan’s Purpose
Before you can effectively stop a threat, you need to understand its intent. Threat scanning isn’t a random act; it’s a purposeful exploration. By recognizing the common motivations behind these scans, you can better tailor your defenses.
Reconnaissance for Exploitation
The most prevalent reason for threat scanning is reconnaissance. Attackers are looking for information. This isn’t just about finding a weak password; it’s about mapping your entire digital landscape.
Identifying Open Ports and Services
Hackers often start by scanning for open ports. These are like doors into your systems. If a port is open and running a service, that service might have its own vulnerabilities that can be exploited. Think of it as someone checking if any doors are unlocked or if any windows are even slightly ajar. The standard ports, like 80 (HTTP) and 443 (HTTPS), are obvious targets, but attackers will also probe less common ports to uncover running services you might have overlooked.
Discovering Operating Systems and Software Versions
Knowing what operating system your servers are running, and the specific versions of the software installed, is vital intelligence for an attacker. Once they know you’re running, say, an outdated version of a particular web server, they can search for known exploits targeting that specific version. This information allows them to move from broad, unfocused scanning to highly targeted attacks. Your systems become a known quantity, and for them, that’s a significant advantage.
Uncovering Exposed Data or Misconfigurations
Beyond technical vulnerabilities, scans can also reveal accidental exposures. This could be a misconfigured cloud storage bucket that’s publicly accessible, an unencrypted database, or sensitive information left in publicly viewable directories. Attackers are looking for low-hanging fruit, and misconfigurations often provide just that. They are essentially looking for digital shortcuts to gain access or steal data without needing to bypass sophisticated security measures.
Preparing for Brute-Force Attacks
Once an attacker has identified potential targets, they might initiate scans to gather information for brute-force attacks. This involves systematically trying a large number of username and password combinations.
Password Spraying Preparation
This is where attackers try a small list of common passwords against a large number of user accounts. If you haven’t properly secured your authentication mechanisms, this can be surprisingly effective. Scans help them identify valid usernames, making the subsequent password-spraying more efficient and less likely to be immediately flagged as suspicious.
Dictionary and Brute-Force Attack Targeting
For specific accounts they believe are valuable, attackers might employ more aggressive dictionary or brute-force attacks. This involves testing thousands or millions of password variations against a single target account. Threat scanning helps them identify which accounts are worth this level of effort.
If you’re looking for effective strategies to stop scanning for threats and enhance your digital security, you might find the article on productivepatty.com particularly helpful. It offers practical tips and insights on how to maintain a secure online environment without the constant worry of potential threats. For more information, you can read the article here: How to Stop Scanning for Threats.
Implementing Proactive Defenses: Your First Line of Action
Stopping threat scanning is a multi-layered approach. It begins with preventing attackers from even getting close enough to scan effectively. This involves hardening your infrastructure and making yourself a less attractive target.
Network Segmentation and Firewalls
Your first and most critical line of defense is a robust firewall. Properly configured firewalls act as gatekeepers, controlling the flow of traffic into and out of your network.
Strict Ingress and Egress Filtering
Don’t just assume your firewall is configured correctly. Regularly review your ingress (inbound) and egress (outbound) filtering rules. Block all unnecessary ports. For services that must be accessible from the internet, restrict access to only the specific IP addresses or ranges that require it. You wouldn’t leave your front door wide open to the public; your network shouldn’t either. For egress filtering, consider what traffic your internal systems are allowed to initiate. This can prevent compromised internal systems from communicating with malicious command-and-control servers.
Demilitarized Zones (DMZs)
For systems that need to be publicly accessible, such as web servers, place them in a DMZ. A DMZ is a separate subnet that sits between your internal network and the external network. This adds an extra layer of protection. If a server in the DMZ is compromised, the attacker is still separated from your critical internal resources by another firewall.
Intrusion Prevention Systems (IPS) and Intrusion Detection Systems (IDS)
These systems are designed to monitor network traffic for malicious activity and can either alert you to threats (IDS) or actively block them (IPS).
Signature-Based Detection
IPS/IDS solutions rely on databases of known malicious patterns (signatures). When traffic matches a signature, the system can either log the event or take action. Keeping these signature databases up-to-date is paramount. The threat landscape evolves rapidly, and your defenses must keep pace.
Anomaly-Based Detection
Beyond signatures, some systems use anomaly-based detection. This involves establishing a baseline of normal network behavior and then alerting on deviations. This can be effective against novel threats that don’t have existing signatures, but it can also generate more false positives. Careful tuning is required.
Network Hardening Techniques: Making Yourself Invisible
Beyond simply blocking access, you can make your network inherently more resilient and less appealing to scanners by implementing sound hardening practices. This is about reducing the attack surface.
Principle of Least Privilege
This fundamental security principle dictates that every user, system, or process should only have the minimum privileges necessary to perform its intended function.
Minimizing Administrative Rights
Avoid granting administrative rights to users or systems unless absolutely essential. The fewer accounts with elevated privileges, the less damage an attacker can do if they compromise an account. Regularly audit who has administrative access and why.
Service Account Management
Service accounts, used by applications or daemons, should also be subject to the principle of least privilege. They should not have broad access to the network or sensitive data. Regularly review the permissions assigned to service accounts.
Regular Patching and Updates
Unpatched vulnerabilities are an open invitation to attackers. Staying on top of software updates is non-negotiable.
Operating System and Application Patching
Establish a regular patching schedule for all operating systems, applications, and firmware. Prioritize critical security patches. Consider automated patching solutions where appropriate, but always test patches in a controlled environment before widespread deployment.
Vulnerability Management Programs
Implement a comprehensive vulnerability management program. This involves regularly scanning your systems for known vulnerabilities and prioritizing remediation efforts based on risk.
Active Defense Against Scanners: Detection and Response
While proactive measures are essential, you also need to be able to detect and respond to ongoing scanning activities. This is where vigilance and the right tools come into play.
Log Management and Analysis
Your systems generate a wealth of information in their logs. Effectively managing and analyzing these logs is critical for identifying suspicious activity.
Centralized Logging
Consolidate logs from all your critical systems into a central logging server or Security Information and Event Management (SIEM) system. This allows you to correlate events across different devices and gain a holistic view of your network activity.
Alerting on Suspicious Patterns
Configure your SIEM or log management system to generate alerts for specific patterns that indicate scanning activity. This could include a high volume of connection attempts to disparate ports, repeated failed login attempts from a single IP, or scans targeting known vulnerable services.
Intrusion Detection Systems (IDS) and Network Traffic Analysis (NTA)
While mentioned earlier for their preventative capabilities, IDS and NTA tools are also crucial for detecting active scanning.
Signature and Anomaly Alerts
Ensure your IDS is configured to alert on known scanning signatures. NTA tools can identify unusual traffic flows that might indicate reconnaissance, even if they don’t match a specific signature. Understanding your baseline network traffic is key to identifying anomalies.
Behavioral Analysis
Look for tools that offer behavioral analysis. These systems can learn what normal network traffic looks like and flag deviations, which is often a tell-tale sign of scanning activity actively probing your defenses.
If you’re looking for effective strategies to stop scanning for threats and enhance your online security, you might find it helpful to explore a related article that offers valuable insights. This resource provides practical tips and techniques to help you focus on more productive activities while ensuring your digital safety. For more information, you can check out this informative piece on productivepatty.com.
Advanced Techniques: Going the Extra Mile
Once you have a solid foundation, you might consider more advanced strategies to further deter and neutralize threat scanners.
Honeypots and Honeynets
These are essentially decoys designed to lure attackers away from your real systems.
Mimicking Real Systems
Set up systems that look like legitimate servers, services, or data repositories, but are isolated and monitored. When an attacker interacts with a honeypot, you gain valuable intelligence about their methods, tools, and motivations without risking your actual assets.
Gathering Threat Intelligence
Honeypots can provide crucial threat intelligence that can be used to improve your overall security posture. You can learn about new attack vectors or the specific types of vulnerabilities being targeted.
Rate Limiting and Blackholing
These techniques involve actively limiting or blocking traffic from suspicious sources.
Connection Rate Limiting
Configure your firewalls or load balancers to limit the number of new connections allowed from a single IP address within a given time frame. This can significantly slow down automated scanning tools.
IP Blackholing (DDoS Mitigation)
In more extreme cases, when a system or network is under a sustained attack or experiencing heavy scanning that’s impacting performance, you might employ IP blackholing. This effectively drops all traffic from a specific IP address or range, albeit temporarily, to alleviate the burden on your resources. This is a more drastic measure and should be carefully considered.
Deception Technology
This is a broader category that includes honeypots but also encompasses other techniques designed to mislead attackers. This could involve deploying deceptive credentials, fake files, or even entire decoy networks. The goal is to waste the attacker’s time and resources while you gather intelligence or even lead them into a controlled environment where their actions can be monitored and neutralized.
Continuous Improvement and Adaptability
The threat landscape is not static, and neither should your security strategy be. The most effective way to stop threat scanning is through a commitment to continuous improvement and adaptability.
Regular Security Audits and Penetration Testing
Don’t assume your defenses are impenetrable. Schedule regular security audits and penetration tests to identify weaknesses that might have emerged or been missed. Treat these tests as real-world scenarios to expose vulnerabilities.
Internal and External Testing
Conduct both internal penetration tests (simulating an attacker with insider access) and external penetration tests (simulating an attacker from the internet). This provides a comprehensive view of your security posture.
Threat Intelligence Integration
Stay informed about the latest threats and vulnerabilities. Integrate threat intelligence feeds into your security tools to ensure your defenses are updated with the most current information. Understanding what adversaries are doing elsewhere can help you prepare for similar attacks.
Vendor Updates and Security Bulletins
Pay close attention to security advisories and bulletins from your software and hardware vendors. They often provide critical information about vulnerabilities and the availability of patches.
Incident Response Planning and Drills
Have a well-defined incident response plan in place. This plan should outline the steps to be taken in the event of a security breach, including how to identify, contain, and eradicate threats. Regularly conduct drills to ensure your team is prepared to execute the plan effectively. This is crucial for minimizing the impact of any successful scan that leads to an exploit. When you see a scan, it’s a precursor to a potential incident. Your response plan needs to be ready.
Stopping threat scanning is not a one-time fix; it’s an ongoing process. By understanding the motivations behind these scans, implementing robust proactive defenses, actively monitoring for suspicious activity, and continuously refining your security posture, you can significantly reduce your exposure and protect your valuable digital assets. It’s about building a resilient and adaptive defense that anticipates and neutralizes threats before they can do real damage. Your commitment to these strategies will ultimately be your strongest shield.
FAQs
What is scanning for threats?
Scanning for threats refers to the process of using security software to search for and identify potential threats, such as viruses, malware, and other malicious software, on a computer or network.
Why is it important to stop scanning for threats?
Stopping scanning for threats is important because it can consume system resources and slow down the performance of the computer or network. Additionally, constant scanning can be disruptive to users and may lead to false positives or unnecessary alerts.
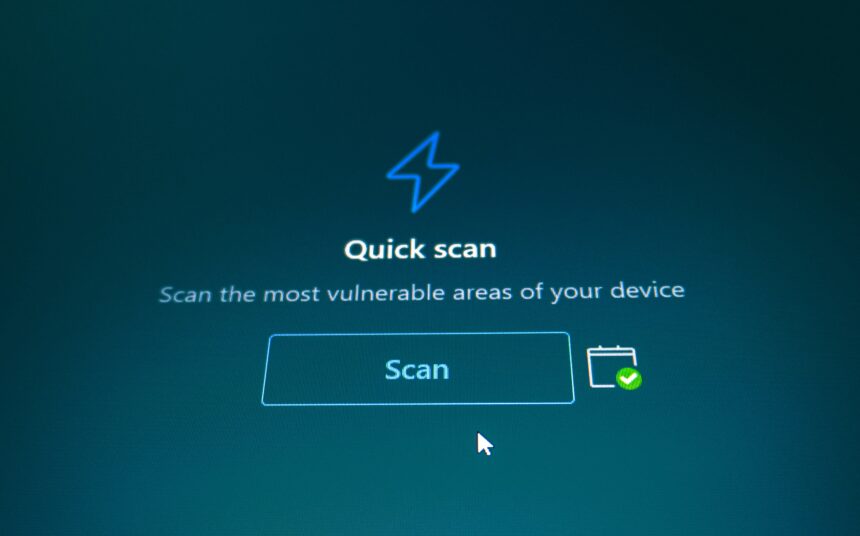
How can I stop scanning for threats?
To stop scanning for threats, you can adjust the settings of your security software to schedule scans for specific times when the computer or network is not in use. You can also configure the software to perform quick scans instead of full system scans, or exclude certain files or folders from being scanned.
What are the potential risks of stopping scanning for threats?
Stopping scanning for threats can leave your computer or network vulnerable to security breaches and infections from viruses, malware, and other malicious software. It is important to find a balance between maintaining security and minimizing the impact on system performance.
Are there alternative methods to prevent security threats without constant scanning?
Yes, there are alternative methods to prevent security threats without constant scanning, such as using real-time protection, keeping software and operating systems updated, practicing safe browsing habits, and implementing network security measures such as firewalls and intrusion detection systems.